Abstract
Information and Communication Technologies (ICTs) and by extension the Internet, have brought immense sociological transformations to humanity. Despite the development the Internet has brought to humanity, the Government of Papua New Guinea (GoPNG) has not lost sight of the fact that the use of ICTs and other related supporting devices are fraught with cybercrime and cyber insecurities that constitute challenges to global law enforcement agencies in PNG and other nations of the world. This paper reports the trends on victims of cybercrimes from 2001 to 2021 and presents an action plan for PNG. The data analysed in this study was explicated from the Internet crime reports published by the Federal Bureau of Investigation and National White Collar Crime Center (IC3). The data were analysed using descriptive statistics and XGraph component of the Statistical Package for Social Sciences’ Population Pyramid. The results confirmed that the number of Internet users that were defrauded increased exponentially from 2016 to 2021. Results from the data explicated from the World Bank on Internet use, revealed that the population of Internet users in PNG and Australia will increase at a minimum rate of 1% to 2% for the next few years. These findings suggest that cybercrimes will be on the rise as the number of Internet users increase at 1% to 2% in PNG and Australia in the next few years. The findings present appropriate strategies to address the incidences of cybercrimes in PNG.
Similar content being viewed by others
Explore related subjects
Discover the latest articles, news and stories from top researchers in related subjects.Avoid common mistakes on your manuscript.
1 Introduction
The incidences of cybercrime have had an astronomical increase due to a myriad of factors in line with increased interconnectivity of the world. The growth of the Internet has brought transformations to every facet of humanity. However, there are two sides of a coin to any development and with technological advancements, cybercrime and lawlessness with Internet use have become a challenge. Notwithstanding the challenges of cybercrimes, Amosun et al. [1] explain that the Internet arose from the computer revolution and is considered the Fourth Industrial Revolution (4IR) advancing educational development, societal development, and societal transformation for humanity.
Ige [2] reports that educational researchers were mid-way into the celebrations of social transformation brought about by the Internet when the anonymity that accompanies Internet use escalated the activities of criminally minded users to harm unsuspecting and novice users. Esen [3] revealed the hydra-headed nature of cybercrime as a new type of criminal activity that lacks globally accepted definition. Illegal activities are conducted using a computer connected to the Internet [4] and the group are referred to in Ige [2] as “new kinds of YakuzaFootnote 1 called Cyber Bandits”.
Scholars confirm that Internet use and development in nations such as Nigeria, South Africa, Cameroon, Ghana, and Togo that have similar developmental indicators as Papua New Guinea (PNG), have experienced cybercrimes that have rarely received governmental intervention due to the technical nature of these crimes and inadequate capacity of the law enforcement agencies to investigate [1, 5]. The crimes committed in the cyberspace by these modern day ‘Yakuzas’ cannot be tried by the traditional laws since these laws were promulgated in the analog era (pre-1980), prior to the widespread commercialisation and global adoption of the Internet in the 1980s and 1990s, making it more accessible to the public.
The objectives of this research are to:
-
Deconstruct the concept of ‘cybercrime’ and cyberspace policing.
-
Explore the trends in the occurrence of cybercrimes in Australia, Fiji, Papua New Guinea, and Australia.
-
Proffer action plans that PNG can adopt to secure the well-being of her citizenry in cyberspace considering cyber breaches and cyber victimisation reported in Australia.
2 Related works
2.1 The concept of ‘cybercrime’
Cybercrime is open to new meaning as it occurs from one nation to another. Evidence from literature shows that the legal framework of a nation or laws promulgated to address cybercrime or strategies adopted by a nation to prevent and address cybercrime, have great influence on the meanings given to or definitions provided, on cybercrimes.
Timofeyev and Dremova [6] consulted Chapter 28 of the Criminal Code in Russia and defined cybercrime as acts that take place in the sphere of information processes that threaten security. In furtherance of the meaning ascribed to cybercrime in The Russian Criminal Code, Timofeyev and Dremova [6] grouped cybercrimes in Russia as follow:
-
Accessing computer information or data illegally,
-
The use of or distribution of malicious programmes,
-
Breaching the rules of storage or processing or transmission of computer information or data, and
-
The spread of pornography [7].
There is no nation of the world that has effectively combated cybercrimes using the criminal code promulgated prior to Internet connectivity gaining momentum across the world. The criminal code adopted by the State Duma in Russia on 24 May 1996, was adopted by the Russian Federation Council on 5 June 1996 and the law was gazetted on 13 June 1996 [7].
However, the Russian Federation lacks the tenacity to prosecute cyber criminals successfully or exhaustively. Timofeyev and Dremova [6] state that Internet use and development in Russia experienced in 1996 has advanced with the Internet becoming more popularised and is wrought with all manner of social, economic, and political activities. Thus, the 1996 laws to address crime occurrences are no longer applicable. The Russian Federation therefore needs to take further steps to enact laws that are specific to crimes committed in cyberspace to protect her citizens. The changing nature of cybercrimes has been facilitated by the advancements of the 4IR, which has challenged law enforcement agents in Russia. From the current realities of cyber lawlessness in Eastern Europe due to the presence of cybercrime hotspots such as Romania and Ukraine that have globally acclaimed computer hackers, there would be criminal occurrences that would demystify the application of these laws specified in The Russian Criminal Code to cybercrimes in future.
The enforcement of law on cybercrimes in Fiji started with the ‘Crimes Decree 2009–Division 6 on Computer Offences’. The use of ‘Decree’ in this cybercrime legislation suggests that these laws were brought into effect during military governance. According to the United Nations Conference on Trade and Development (UNCTD) [8], Fiji is one of the 46 countries in the Asia–Pacific region that has cybercrime legislation while seven have draft legislations, and seven have no legislation on cybercrime.
The Cybercrime Act enacted in Fiji in 2021, states that cybercrime is the use of computer systems to:
-
compromise the confidentiality, integrity, and availability of computer data and computer systems;
-
commit computer-related forgery, computer-related extortion, and computer-related fraud; and
-
commit other non-computer dependent offences such as identity theft, and telecommunications services theft [9].
The Cybercrime Act promulgated in Fiji accommodates cooperation and collaboration with the governments of other countries to ensuring that stored computer data is accessible to cross-border entities for investigative purposes. The Fijian Cybercrime Act (2021) empowers the supervisory minister to prescribe penalties that do not exceed FJD50000.00 and FJD200000.00 for individual and corporate entities that violate the provisions of this ‘Act’.
Cybercrime in Australia refers to the use of computers and other related devices (that is, ancillary) to commit serious commonwealth, state, or territory-related offences [10]. The Australian Cybercrime Act (ACA) went into effect in 2001 and was amended by Act No. 127 of 2004. The promulgation of Cybercrime Act in 2001 amended or repealed the relevant sections of certain laws that were improvised to address cybercrimes in Australia; these included Crimes Act 1914, Customs Act 1901, Telecommunications (Interception) Act 1979, Australian Security Intelligence Organisation Act 1979, Criminal Code Act 1995, and Education Services Student Act 2000 [10]. These amendments, or repealments of these laws with the enactment of Cybercrime Act in 2001 in Australia, suggests the legal complexities of different laws to address cybercrimes on the Internet or 4IR era.
The provisions of Cybercrime Code Act 2016 in Papua New Guinea, lists four divisions of activities that constitute cybercrimes:
2.2 Division 1: offences related to the integrity of data and electronic systems or devices
-
Unauthorised access or hacking
-
Illegal interception
-
Data interference
-
System interference
-
Data espionage
-
Illegally remaining.
2.3 Division 2: computer related offences
-
Electronic fraud
-
Electronic forgery
-
Electronic gambling or lottery by a child
-
Identity theft
-
Illegal devices.
2.4 Division 3: content related offences
-
Pornography
-
Child pornography
-
Child online grooming
-
Animal pornography
-
Defamatory publication
-
Cyber bullying
-
Cyber harassment
-
Cyber extortion
-
Unlawful disclosure
-
Spam.
2.5 Division 4: other offences
-
Cyber attack
-
Online copyright infringement
-
Online trademark infringement
-
Patent and industrial designs infringement
-
Unlawful advertising.Footnote 2
The cybercrime laws enacted in Russia, Fiji, and Australia that were reviewed in this study are comparable to the provisions of the Papua New Guinea’s Cybercrime Code Act that was passed in 2016. Additionally, the cybercrime law enforcements in Russia, Fiji, and Australia have legal structures that collaborates on investigation of crimes in their cyberspace and cyberspace of other countries of the world that requires technical and investigative assistance to prosecute cyber lawlessness.
2.6 Incidences of cybercrimes in Papua New Guinea
The incidences of cybercrimes reported and prosecuted in PNG are ‘content-related offences’Footnote 3 and not financial related crimes like the cases reported by IC3 in Australia and other countries.
It was reported that a man known as ‘Dominic Aku’ from the Eastern Highlands of PNG adopted the nom de guerre ‘Jason Aku’ to post a threat about Prime Minister Marape in 2020 from the prison at Bomana.Footnote 4 In 2020, Ronald Katak of Nelikum village in East Sepik of PNG was arrested by the investigators of the Royal Papua New Guinea Constabulary (RPNGC)’s cybercrime unit for posting defamatory statements about the Agriculture Minister of PNG on Facebook.Footnote 5 These cases reported in PNG are before the courts since the matters violated the provisions of Cybercrime Code Act 2016. The interesting aspect of crimes committed in the cyberspace in PNG is the culture of settling such disputes out of courts for compensations related benefits.Footnote 6 In developed nations of the world, the cybercrime case reported in East Sepik could suffer a setback in court since it is related to freedom of information and speech due to the involvement of a political office holder that is currently serving in the government.
2.7 Cyberspace policing
The uniqueness of crimes committed in cyberspace necessitated the use of different approaches to protect users and information in cyberspace. Cyberspace is open to diverse attacks from web-based criminals, terrorists, and hackers located in different countries of the world [11]. Tropina [12] argues that the use of new technologies has created new possibilities for criminals to exploit the same advantages offered by the new technologies. This emerging scenario led some nations to design lawful strategies for policing cyberspace. At present, cyberspace remains the prominent source of innumerable ‘’against the law” activities such as the dark web commercial transactions, child pornography, hacking, and migration of traditional crimes such as advanced fee fraud (419), copyright infringements, and disruption of ICT networks [12].
In 2022, the incidences of cybercrimes have grown by 13% to 76,000 in one year, which implies that cybercrime is committed every seven minutes in Australia [13]. The evolving threats from the crimes committed in cyberspace led stakeholders in Australia to declare that “cyberspace has become a battleground” and is “increasingly the domain of warfare” [13]. In 2023, the Australian High Tech Crime Centre (AHTCC) was founded and hosted in Canberra by the Australian Federal Police (AFP). The AHTCC transformed into a new High Tech Crime Operations (HTCO) portfolio in 2007 and was officially launched in 2008 [14]. The new HTCO is saddled with the responsibility of investigating online child sex exploitation, collaborating with banking and finance institutions on protection from cyber-attack, protection of Australia’s information infrastructure, and countering forms of crimes enabled by technology [14]. Besides Australia, the United States, the United Kingdom, Canada, India, and France have specialized organizations that maintain law and order in cyberspace other than the national police [15].
A new dimension of cyberspace policing in India called “Cyber Hawks” evolved in July 2022. The “Cyber Hawks” comprises 30 top social media influencers (i.e., civilians) that have agreed to work with a city police chief called “Chief Amitech Kumar” in Nagpur, India [16]. The 30 cyber hawks will patrol cyberspace as volunteers by assisting the police in Nagpurto generate local feeds on online content platforms and their contents [16]. Despite the promises presented by informal or formal strategies adopted by some countries of the world on cyberspace policing, scholars have identified these primary challenges to policing cyberspace:
-
1.
The anonymity offered by the Internet enables cyber scammers to commit crimes at geographical locations when they are not physically residing or present [2].
-
2.
The cross-jurisdictional presence of the perpetrator makes cyber policing difficult especially if the perpetrator is anonymous [17].
-
3.
Enmity or hostility between countries [18] could hinder collaboration on tackling or countering cybercrimes across transnational borders. Chang [18] reported that there were computer attacks completed against the United States of America that originated from computers in Taiwan but controlled by command-and-control servers in China.
Notwithstanding the highlighted challenges, police, and cyberspace researchers such as Aremu [19], Broadhurst [20], Choo [21], and Jaishankar [22] should note that cyberspace has emerged as the cosmopolitan frontier of information age policing (See Sampson [23]). Now, cybercrime has transformed into a growing social and financial problem [24].
3 Materials and methods
3.1 Data for the study
The data analysed to explore the occurrence of cybercrimes in Australia from 2001 to 2021 were taken from the Internet Crime Reports (Formerly Internet Fraud Reports), compiled by The Federal Bureau of Investigation’s (FBI) Internet Crime Complaint Center (IFCC) created by the United States (US) government to collect data on a new variant of criminal activity emerging in the 2000s [25].
From 8 May 2000 to 31 December 2021, the complaints received by the Internet Crime Complaint Center (IC3) exceeded 6.5 million [26]. The Federal Bureau of Investigation (2021) explains that the data provided in the annual reports are aggregated to promote public awareness and educate the public on trends inherent in cyber and Internet crimes to enable different nationalities to stay ahead of threats posed by this new type of criminal activity.
The data presented on incidences of cybercrimes in this study were accessed and extracted from the Internet Fraud and Crime Reports of 2001 to 2021 [26] as well as the institutional website of National White Collar Crime Center [26].
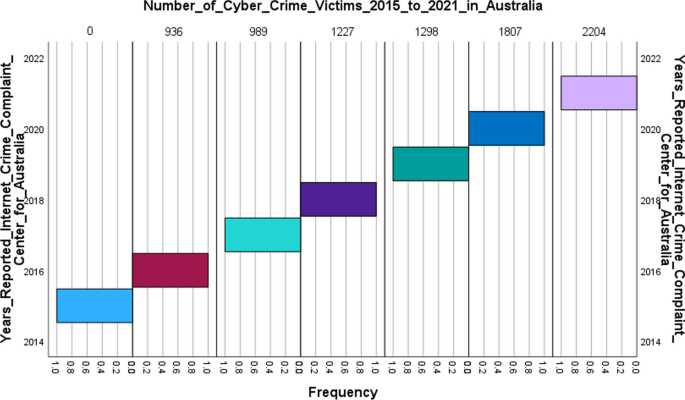
3.2 Analysis of data on cybercrimes
The data were analysed using descriptive statistics to highlight the trends inherent in cybercrime occurrences in Australia from 2001 to 2021. Percentages, XGraph of Population Pyramid on IBM Statistical Package for Social Sciences (SPSS) 29.0 were used to present the trends. The two outputs of XGraph generated by the Population Pyramid program were screened by three academic researchers (two male, one female) to select the output most friendly to non-mathematically inclined readers of the National Research Institute’s publications. The output of XGraph, selected by two (one male, one female) of the three selected academic researchers, is presented Figs. 1 and 2 in the section on results of the study. The data analysed were used to make future projections on the nature and dimension of cybercrimes that Papua New Guinea could experience in the future.
4 Results
4.1 Trends in the occurrence of cybercrimes in Australia
The data extracted from the Internet crime reports for this study were coded and analysed in two parts because:
-
The data released by The Federal Bureau of Investigation and National White Collar Crime Center from 2001 to 2015 were presented in percentages.
-
The total complaints received from Internet users used to calculate these statistics were presented in the annual reports on Internet crime.
-
The data released by The Federal Bureau of Investigation and National White Collar Crime Center in 2000 only comprised the total number of complaints with summary details.
-
From 2016 to 2021, the IC3 discontinued the use of statistical percentages, and presented the number of victims in each country of the world reported in whole numbers.
The results of the analysis are presented in the following figures.
The analysed data presented in Fig. 1, indicates that for the first time Australia featured at the list of top ten nations whose citizens were victimised in cyberspace in 2001.
The number of people in Australia that lost funds to cyber criminals rose astronomically from 2001 to 2005 but declined from 2006 to 2009. The trend went up in 2010 to 0.7% (4th) and declined gradually from 2011 to 2014 (0.53%; 5th). In 2015, 288,012 victims were defrauded via the Internet globally; however, Australia did not feature in the global top ten countries listed in that year.
The results presented in Fig. 2 show the increase in the number of cybercrime victims located in Australia from 2016, that resulted in the country being listed in the top ten global ranking in 2016.
(936)→ 2017 (989)→ 2018 (1227)→ 2019 (1298)→ 2020 (1807)→ 2021 (2204).
For these years, Australia was in 5th, 6th, and 4th place respectively. A striking trend in the data presented by the National White Collar Crime Center and the Federal Bureau of Investigation from 2016 to 2019, is that Australia occupied the 5th position consecutively among the global nations with cybercrime victims. The statistics provided below Fig. 2 show a steady increase in the number of cybercrime victims, despite the fifth position occupied by Australia for these years.
5 Discussion
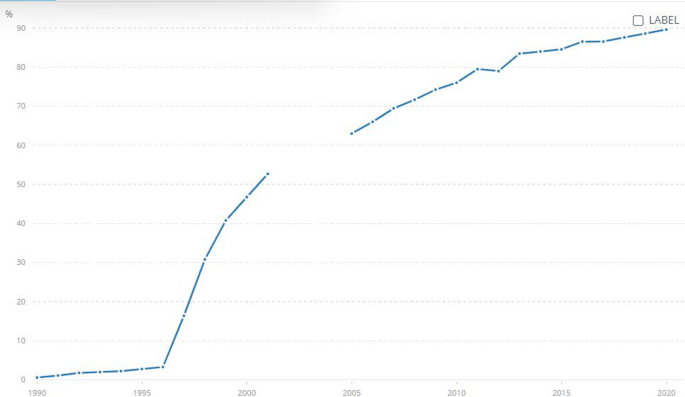
The trends inherent or observable in the data extracted on cybercrimes in Australia confirms that incidences of crimes in cyberspace have escalated from 2016 to 2021. A plausible explanation for the steady increase in the number of victims of cybercrimes in Australia seems attributable to the increase in the number of individuals using the Internet in the country. The data presented by the World Bank [27] in Fig. 3 indicates that 85% of the population in Australia used the Internet in 2015, this statistic increased to 87% of the Australian population in 2016 and steadied at 87% in 2017.
Statistics of individual internet users in Australia 1990 to 2020 [46]
The percentage of Internet users increased to 88% in 2018, and by 2019, it had reached 89%. Internet users among the total residents in Australia stood at 90% in 2020. Data provided by the World Bank [27] indicated that the population of Australia in 2021 was 25,739,256Footnote 7; however, only 1,022,449 had access to the 39,794 secure Internet servers reported in the data. The implication of these statistics is that if Internet access continues to grow at 1% for the next 10 years, Australia could experience cyberattacks that would lead to an astronomical increase in the number of cybercrime victims reported to the National White Collar Crime Center for Australia.
However, the inference drawn regarding escalating cyber victimisation would be moderated if an increased proportion of Internet users in Australia have access to secure Internet servers. This has not been the case, as indicted by data presented by the World Bank [28] in Fig. 4.
Secure internet users in Australia 1990 to 2020 [46]
As at 2020 (i.e., latest/current data), there were 39,794 secure Internet servers per 1 million people residing in Australia. This implies that there are close to 960,206 vulnerable Internet users per one million residents in Australia, and 24,716,807 in general in this same country [29]. This information is a further technical-related reason for escalating cyber victimisation of unsuspecting Internet users in Australia.
Ezebilo and Kipongi [30] affirm that government effectiveness in the provision of public goods and services is vital for economic growth, and this includes the use of technology and the advantages of its development. Of importance, therefore, is cybersecurity particularly with increasing interconnectivity among countries in the world. According to the Federal Bureau of Investigation and the National White Collar Crime Center [31], the monetary losses attributed to Internet-related scams that have affected citizens of different countries of the world, including Australia from 2017 to 2021, stood at $18.7 billion. The Federal Bureau of Investigation and the National White Collar Crime Center [31] thus confirm cybersecurity as one of the essential goods and services of a public nature necessary in all countries of the world.
5.1 Applicability of cybercrime occurrences in Australia to Papua New Guinea
The statistics on Australia presented by the FBI and IC3 regarding the incidences of cybercrimes, are applicable to Papua New Guinea (PNG) because the number of Internet users in both countries has increased at 1% to 2% from 2013 to 2017. The 2018 to 2020 data on the growth in the population of Internet users has not been computed and this non-availability of data applies to available secure Internet users for PNG as well.
Other motivations for studying occurrences of cybercrime and using it as a benchmark for PNG is the geographical proximity of the two nations. For instance, only 4 km separates Australia and PNG in the Torres Strait, a transitionary boundary that was redefined till 1985 [32]. There are possibilities that cyber breaches in Australia pose great risks to the security of cyber infrastructures in PNG since geographical proximity, cultural connections and Australians-Papua New Guineans interactions goes back to premodern era.Footnote 8
Predictions are that the use of mobile phones in PNG could rise from 2.5 million to 6 million within 5 years [33] and would be accompanied with subscriptions to data services by PNG citizens, which have the potential to expose PNG citizens to cybercriminals. PNG had 1.37 million Internet users in January 2021, which marked an increase of 270,000 from year 2020 [34]. The rate at which Internet users are on the rise in PNG calls for a proactive approach from the government and law enforcement agencies on securing the activities involving her citizenry in cyberspace.
In PNG at present, there are challenges experienced on investigating transnational crimes while the incidences of crimes do not match or correspond to arrests and convictions made by the Royal Papua New Guinea Constabulary (RPNGC) [35]. Considering security risks that are associated with increased interconnectivity of PNG and her virtual assets, the GoPNG must develop a cyberspace policy that reflects PNG’s vital intercultural values and unhindered transmission of information. This cyberspace policy must adopt a holistic approach to PNG’s citizenry e-welfare that includes protection against all forms of crimes in cyberspace.
According to the United States Government [36], cyberspace norms should be supported by the following principles: upholding fundamental freedoms, respect for property, valuing privacy, protection from crime, and right of self-defence. A cursory evaluation of these fundamental principles that the United States affirms, is a fundamental strategic plan for strategies that could enable a state to meet her traditional international obligations. It confirms that common principles necessary for a just society in the physical space, are also applicable to man’s existence and interaction in cyberspace.
The task of developing a cyberspace policy for PNG needs consultation or support of other nations, especially countries with advanced mechanisms for combating cybercrimes. The contents of the proposed PNG’s cyberspace policy must align with her foreign policy. For instance, in the case of United States, this country will, along with other countries of the world, encourage responsible behaviour and oppose people that seek to disrupt networks and systems, divert, and deter malicious actors, and preserve the United States’ vital national assets as necessary and appropriate [36]. In 2016, PNG promulgated the Cybercrime Code to tackle the occurrences of crimes in the cyberspace and in 2021, PNG developed a cybersecurity policy with the aim of demonstrating government’s commitment to strengthen the GoPNG cybersecurity capabilities or know-how and preserve PNG from cyber threats.Footnote 9 Despite the importance of these documents to e-citizenship in PNG, an international strategy for the cyberspace is needed to establish the policy priorities for PNG regarding the use of cyberspace.
5.2 Action plan on cybersecurity for Papua New Guinea
The Government of Papua New Guinea (GoPNG) could adopt certain strategies to outmanoeuvre cybercriminals or terrorist groups targeting the PNG citizenry. The United States International Strategy for Cyberspace [36] recognises that threats to Internet networks are constituted by terrorists, cybercriminals, states, and proxies (Agents) of cybercriminals or states. The United States International Strategy for Cyberspace [36] also recognises another interest group in the cyberspace called the ‘good actors’. The good actors in the context of this study are individuals, governmental, non-governmental and social entities that promote civil liberties, privacy, cross-cultural and transnational values in the cyberspace. One of the modern strategies of combating occurrences of crimes in cyberspace is ‘Cyberspace Policing or Cyberspace Constabulary’.
5.3 Cyberspace policing or cyberspace constabulary
Cyberspace policing is the use of police in the real world to secure human beings that transact different activities in cyberspace and tackle criminality and ill-social behaviours in the online or virtual world. Cyberspace has been described as the new frontier for policing [37]. This conception was made by Sampson [37] as the rise or evolution of cyberspace has created new types of criminal activities and varieties of anti-social behaviours that humanity has not witnessed prior to the Internet era. Cyberspace policing must be considered by state actors as a core responsibility of the government, and not an aspect of a societal life that can be outsourced to private Internet security companies. The severity and hydra-headed nature of cybercrimes has led to the formation of different bodies or interest groups to secure the cyberspace, notably ‘The Society for the Policing of Cyberspace’.Footnote 10
The PNG Cyberspace Police could be equipped to effectively maintain law and order in the PNG’s cyberspace by designing a web portal. The web portal must feature questions that will enable the PNG Cyberspace Police to seamlessly transfer cases or incidences beyond their technical capacity to resolve to The Federal Bureau of Investigation (FBI) and the Australian Cyber Security CentreFootnote 11 (ACSC). The essential questions on the web portal must have the biographical information of the cybercrime victim such as: Name, Sex, Age, City of Residence, Province, Country, Mobile Number, Email Address, as well as the complaint.
Other primary questions that would enable the victims to provide information for investigative or reporting purposes for the PNG Cyberspace Police are also necessary for the effective use of the PNG Cyberspace Police web portal (see Appendix). There are other interest groups beside institutionalised cyberspace police in different nations of the world, such as cyberspace vigilantes. These cyberspace vigilantes adopt legal and illegal approaches to attain their objectives of securing cyberspace. However, the illegal dimensions of cyberspace vigilantes make it undesirable as an approach to administer or attain justice in the PNG cyberspace.
5.4 The PNG cyberspace asset recovery team
Another component of the action plan that PNG can adopt to tackle crime occurrences in cyberspace is to constitute the PNG Cyberspace Asset Recovery Team (PNGCART) [38]. The Recovery Asset Model (RAT) was developed and used by the United States Internet Crime Complaint Center (IC3) to connect law enforcement agencies and financial institutions to support statistical and investigative analyses. According to the Federal Bureau of Investigation and National White Collar Crime Center [31], the IC3’s RAT was designed to rationalise communication with financial institutions and enable the Federal Bureau of Investigation’s structures to freeze funds and possibly accounts of victims that have made transfers or payments to domestic accounts under false and fraudulent premises.
The GoPNG can develop or replicate the IC3’s RAT, as presented in Fig. 5.
Once a complaint is logged through the crime complaint centre, it is recorded in the PNG Cyberspace Police database. The automated triage provides instant digital evidence which is interpreted and analysed by the expertise of Computer Science analysts. This means that complaints received from the public could be assigned to their investigative officers with the PNGCART acting as an electronic liaison between the RPNGC and financial institutions supporting statistical and investigative analyses in PNG.
5.5 Education for justice
The Education for Justice (E4J) was initiated and developed by the United Nations Office on Drugs and Crime (UNODC) in partnership with The United Nations Educational, Scientific and Cultural Organisation (UNESCO) [39]. The E4J aims to foster or advance crime prevention and culture of lawfulness through educational activities designed for different levels of education, such as primary, secondary, and tertiary. The resources provided by the E4J team are useful to teach the rule of law and suitable for cybersecurity education for learners in primary, secondary, and higher educational institutions.
In the section of E4J/UNODC website developed for primary school learners there is a ‘Fun Corner’, ‘Primary-Level Library of Resources’, and ‘E4J Tools and Lesson Plans’ [40]. These resources feature educational materials appropriate for primary school learners on issues related to law for policy makers, teachers, parents, and students. The E4J tools and lesson plans have diverse resources for stakeholders that would enable them to facilitate lessons, workshops or training programmes on conflict resolution, critical thinking, teamwork, and empathy.
Another section of the E4J/UNODC website provides resources for secondary education [41]. This section contains a developed resource guide to support the Model United Nations (MUN) conference organisers on featuring issues emanating from UNODC foci into academic conferences. A unique feature of this section is the non-electronic game-based learning materials developed for 13–18-year-old learners, focusing on rule of law-related topics. Additionally, this section features handbooks developed for teachers in secondary and primary schools to support the teaching of rule of law-related topics. Finally, a further section on the E4J/UNODC website provides an array of peer-reviewed university teaching modules developed by 600 academics in more than 550 universities and 114 countries for teaching global crime prevention, integrity, and ethics [42].
6 Conclusion
This study investigated the trends on victims of cybercrime from 2001 to 2021 drawing on data provided by the Federal Bureau of Investigation and the National White Collar Crime Center. The outcomes of the literature reviewed, and data explicated from the repositories of the Federal Bureau of Investigation and the National White Collar Crime Center project the trends of cyber-victimisation experienced by citizens of Australia.
The data explicated from the World Bank confirms that Internet use and access in Australia and Papua New Guinea are growing annually at 1% to 2%. This data confirms that PNG will be more interconnected in the next few years. The increased interconnectivity of PNG needs adequate planning or measures on cybersecurity as Internet users in PNG become vulnerable to cyber scammers. Part of the cybersecurity measures for GoPNG is to invest in secured Internet servers for the emerging Internet users in PNG. Another veritable reason that justifies the need for institutionalised cybersecurity education in PNG, is the uniqueness of the nation as the primary bridge to the Pacific and South East Asia due to its strategic geographical location.
The lesson evident in the occurrence of cybercrimes in Australia is that none of the developed nations have effectively combated cybercrimes using the criminal code or provisions that were enacted during the analog era. The GoPNG should align or streamline the activities of organisations such as PNG Computer Emergency Response Team (PNGCERT), PNG National Cyber Security Centre (PNGNCSC), and the Cybercrime Unit of the Royal PNG Constabulary (RPNGC). The streamlining of the activities of these organisations would enable the Government to have a robust national cybersecurity plan in place for the country. This coordinated approach would transform PNG to the hub of cybersecurity in the Asia–Pacific region. The findings of this research would empower policy makers and cybersecurity experts to identify the appropriate national approach of furthering PNG cybersecurity agenda and reduce occurrences of cybercrimes in PNG.
Data availability
The data used for this study are publicly available at https://www.ic3.gov/Home/AnnualReports
Notes
Members of transnational organised crime syndicates originating in Japan.
See [43].
See [44].
See Data Catalog (worldbank.org) [46].
Cyber Security Policy 2021 – DICT I PNG.
https://www.dfat.gov.au/geo/torres-strait/the-torres-strait-treaty [48]. The Torres Strait Treaty defines the border between Australia and Papua New Guinea and provides a framework for the management of the common border area.
See polycyb.org.
See ic3.gov and cyber.gov.au.
Abbreviations
- 4IR:
-
Fourth Industrial Revolution
- ACA:
-
Australian Cybercrime Act
- ACSC:
-
Australian Cyber Security Centre (see https://www.ic3.gov/ and Home | Cyber.gov.au)
- E4J:
-
Education for Justice
- FBI:
-
Federal Bureau of Investigation
- DFAT:
-
Australian Government Department of Foreign Affairs and Trade
- GoPNG:
-
Government of Papua New Guinea
- IC3:
-
Internet Crime Complaint Center
- DICT I PNG:
-
Papua New Guinea Department of Information and Communications Technology
- IFCC:
-
Internet Crime Complaint Center/Internet Fraud Complaint Center
- MUN:
-
Model United Nations
- PNG:
-
Papua New Guinea
- PNGCART:
-
Papua New Guinea Cyberspace Asset Recovery Team
- RPNGC:
-
Royal Papua New Guinea Constabulary
- PNGNCSC:
-
PNG National Cyber Security Centre
- RAT:
-
Recovery Asset Model
- SPSS:
-
Statistical Package for Social Sciences
- UNCTD:
-
United Nations Conference on Trade and Development
- UNESCO:
-
United Nations Educational, Scientific and Cultural Organisation
- UNODC:
-
United Nations Office on Drugs and Crime
- US:
-
United States
References
Amosun PA, Ige OA, Choo KKR. Impact of a participatory cyber crime prevention programme on secondary school students’ attainment in crime prevention concepts in civic education and social studies. Educ Inf Technol. 2015;20:505–18. https://doi.org/10.1007/s10639-013-9298-0.
Ige OA. Effects of gender and technological fluency on learners’ attitude to cyber crime prevention in urban learning ecologies: lessons for Swedish gymnasiums. Int J Cyber Criminol. 2018;12:151.
Esen R. Cybercrime: a growing problem. J Crim Law. 2002;66(3):269–83.
Amosun PA, Ige OA. Internet crime: a new breed of crime among in-school aged children in Nigeria. The African Symposium, (ISSN# TX 6-342-323) 2009;9(2): 90–98.
Adu, E.O., Ige, O.A. Secondary School Teachers’ Perceptions of Incidences of Cyber Crimes among School-aged Children in Lagos State, Nigeria. In J.F. Van Niekerk (Eds.), Proceedings of the African Cyber Citizenship Conference 2016 (ACCC2016). Nelson Mandela Metropolitan University, Port Elizabeth. 2016; ISBN: 978-1-920508-74-6.http://accconference.mandela.ac.za/ACCConference/media/Store/images/Proceedings-2016-v3_1.pdf.
Timofeyev Y, Dremova O. Insurers’ responses to cyber crime: evidence from Russia. Int J Law Crime Justice. 2022. https://doi.org/10.1016/j.ijlcj.2021.100520.
The Russian Federation. The Criminal Code of The Russian Federation No. 63-Fz of June 13, 1996. https://www.wipo.int/edocs/lexdocs/laws/en/ru/ru080en.pdf. Accessed 3 Nov 2022.
United Nations Conference on Trade and Development (UNCTD). Cybercrime legislation worldwide. 2022. Cybercrime Legislation Worldwide | UNCTAD. Accessed 8 Feb 2023.
Office of the Attorney General, Fiji. The Laws of Fiji: Cybercrime act 2021. 2019; https://laws.gov.fj/Acts/DisplayAct/3165#. Accessed 3 Nov 2022.
The Australian Government. Cybercrime Act 2001 Act No. 161 of 2001 as amended. 2004. https://rm.coe.int/cybercrime-act-2001/16808e70b4. Accessed 3 Nov 2022.
Baraz A, Montasari R. Law enforcement and the policing of cyberspace. In: Montasari R, Carpenter V, Masys AJ, editors. Digital transformation in policing: the promise perils and solutions. Advanced sciences and technologies for security applications. Cham: Springer; 2023. https://doi.org/10.1007/978-3-031-09691-4_4.
Tropina T. Cyber-policing: the role of the police in fighting cybercrime. 2017. Special Issue 2 Eur. Police Sci Res Bull. 287.
Hurst, D. 3 November 2022. Cyberspace ‘a battleground’ as reports of cybercrime in Australia jump 13%. https://www.theguardian.com/australia-news/2022/nov/04/cyberspace-a-battleground-as-reports-of-cybercrime-in-australia-jump-13. Accessed 26 July 2023.
The Australian Federal Police. High Tech Crime: AFP casts a wide Net. https://www.afp.gov.au/sites/default/files/PDF/high-tech-crime-afp-casts-a-wide-net.pdf. Accessed 26 July 2023.
Ige OA. Promoting the cyber wellness of internet users in Papua New Guinea. E J Humanit Arts Soc Sci. 2023;4(3):276–86. https://doi.org/10.38159/ehass.2023438.
Soumitra, B. Maharashtra police creates team of 30 cyber hawks to patrol. 18 July 2022. The Times of India. Maharashtra police creates team of 30 cyber hawks to patrol cyberspace | Nagpur News - Times of India (indiatimes.com). Accessed 26 July 2023
Mehta, A. Module 32: Cyber Policing and Cyber Crime Investigation. 2013. 1521181215E-Text-CyberPolicing.pdf (inflibnet.ac.in). Accessed 27 July 2023.
Chang LYC. Formal and informal modalities for policing cybercrime across the Taiwan Strait. Polic Soc. 2013;23(4):540–55. https://doi.org/10.1080/10439463.2013.780221.
Aremu, O. The ’trinity’ and the Missing Mission in Policing: An Inaugural Lecture delivered at the University of Ibadan. 18 May 2017.
Broadhurst, R. Cybercrime in Australia. 6 November 2016. Roderic B. Cybercrime. 2017. The Australian and New Zealand Handbook of Criminology, Crime, and Justice, Deckert, Antje, and Richard Sarre Eds. Palgrave McMillan: Chapter 19, https://ssrn.com/abstract=2865295.
Choo KKR. The cyber threat landscape: challenges and future research directions. Comput Secur. 2011;30(8):719–31. https://doi.org/10.1016/j.cose.2011.08.004.
Jaishankar K. Space transition theory of cyber crimes. In: Schmallager F, Pittaro M, editors. Crimes of the internet. Upper Saddle River: Prentice Hall; 2008. p. 283–301.
Sampson F. Chapter 1 - Cyberspace: The new frontier for policing? In: Akhgar B, Staniforth A, Bosco F, editors. Cyber crime and cyber terrorism investigator’s handbook. Oxford: Syngress; 2014. p. 1–10. https://doi.org/10.1016/B978-0-12-800743-3.00001-3.
Wilson M, Cross C, Holt T, Powell A. Police preparedness to respond to cybercrime in Australia: an analysis of individual and organizational capabilities. J Criminol. 2022;55(4):468–94. https://doi.org/10.1177/26338076221123080.
The Federal Bureau of Investigation National Press Office. The FBI’s Internet Crime Complaint Center (IC3) marks its 20th year. 2020. https://www.ic3.gov/Media/PDF/AnnualReport/2021IC3Report.pdf
The Federal Bureau of Investigation Internet Crime Complaint Center (IC3). 2001–2022. Annual reports. https://www.ic3.gov/Home/AnnualReports.
The World Bank. Individuals using the Internet (% of population) - Australia 1990 to 2020. 2020. https://data.worldbank.org/. Accessed 12 Dec 2022.
The World Bank. Secure Internet servers - Australia 1990 to 2020. 2020. https://data.worldbank.org/. Accessed 12 Dec 2022.
The World Bank. Secure Internet servers (per 1 million people) - Australia 1990 to 2020. 2020. https://data.worldbank.org/. Accessed 12 Dec 2022.
Ezebilo, E.E. & Kipongi, W. Comparative analysis of governance and economic growth in Fiji, Papua New Guinea, Solomon Islands, and Vanuatu. 2022; Discussion Paper No. 196 June 2022. The National Research Institute, Papua New Guinea.
The Federal Bureau of Investigation Internet Crime Complaint Center (IC3). 2022. Annual reports. https://www.ic3.gov/Home/AnnualReports.
O'Brien, P.A. If Papua New Guinea really is part of Australia’s ‘family’, we’d do well to remember our shared history. 2021. If Papua New Guinea really is part of Australia's 'family', we'd do well to remember our shared history (theconversation.com). Accessed 21 June 2023
The National Tech Pacific. (2022). Mobile Phone usage in Papua New Guinea predicted to rise. Mobile Phone usage in Papua New Guinea predicted to rise - Tech Pacific (pngfacts.com). Accessed 12 Dec 2022.
Kemp, S. Digital 2021: Papua New Guinea. Digital in Papua New Guinea: All the Statistics You Need in 202.12 February 2021. — DataReportal – Global Digital Insights.
Finkeo, M. Yamasombi: Focus on transnational and cyber crime. 2022. Post Courier Yamasombi: Focus on transnational and cyber crime. Accessed 12 Dec 2022.
The United States Government. United States International Strategy for Cyberspace: Prosperity, Security, and Openness in a Networked World. 2011. international_strategy_for_cyberspace.pdf (archives.gov). Accessed 12 Dec 2022.
Sampson, F. (2014). Chapter 1 – Cyberspace: The new frontier for policing? Cyber Crime and Cyber Terrorism Investigator’s Handbook. https://doi.org/10.1016/C2013-0-15338-X.
Ige, O.A. Strategies for combating cybercrimes in Papua New Guinea. 2022; Spotlight, 15(23): 1–5. The National Research Institute, Papua New Guinea.
United Nations Office on Drugs and Crime (UNODC). Tertiary education. Secondary education. 2015. Tertiary Education (unodc.org). Accessed 12 Dec 2022.
United Nations Office on Drugs and Crime (UNODC). Education for Justice. 2015. Education for Justice (unodc.org). Accessed 2 Dec 2022.
United Nations Office on Drugs and Crime (UNODC). Primary education. 2015. Primary Education (unodc.org). Accessed 12 Dec 2022.
United Nations Office on Drugs and Crime (UNODC). Secondary education. Secondary education. 2015. Secondary Education (unodc.org). Accessed 12 Dec 2022.
The Papua New Guinea Government. Cybercrime code act 2016. 2016. https://www.nicta.gov.pg/regulatory/internet/cybercrime-cybersecurity/
The National News. Several cybercrime cases before the courts. 2021. Several cyber crime cases before court - Post Courier. Accessed 21 June 2023
Papua New Guinea Today. East Sepik 1st Cybercrime case. 2020. East Sepik Province 1st Cybercrime case - Papua New Guinea Today (pngfacts.com). Accessed 21 June 2023.
The World Bank. Data Catalog. 2022. Data Catalog (worldbank.org). Accessed 12 Dec 2022.
High Commission of The Independent State of Papua New Guinea, Canberra, Australia. Relationship with Australia. Relationship with Australia – High Commission of the Independent State of Papua New Guinea (pngcanberra.org). Accessed 21 June 2023
Department of Foreign Affairs and Trade, Australian Government. The Torres Strait Treaty. https://www.dfat.gov.au/geo/torres-strait/the-torres-strait-treaty. Accessed 28 June 2023.
Author information
Authors and Affiliations
Contributions
OI extracted the data, analysed the data, and wrote the manuscript.
Corresponding author
Ethics declarations
Ethics approval and consent to participate
This research manuscript does not contain any studies with human participants performed by the author. The data used analysed and presented in the manuscript are open and publicly available.
Informed consent
This research manuscript does not contain any studies with human participants performed by the author.
Competing interests
The author declares that there are no competing interests in the completion of this research.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Appendix: Essential Questions for PNG Cyberspace Police web portal
Appendix: Essential Questions for PNG Cyberspace Police web portal

Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made. The images or other third party material in this article are included in the article's Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article's Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Ige, O. Trends of cybercrime from 2001 to 2021: cybersecurity action plan for Papua New Guinea. Discov glob soc 1, 9 (2023). https://doi.org/10.1007/s44282-023-00007-7
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s44282-023-00007-7